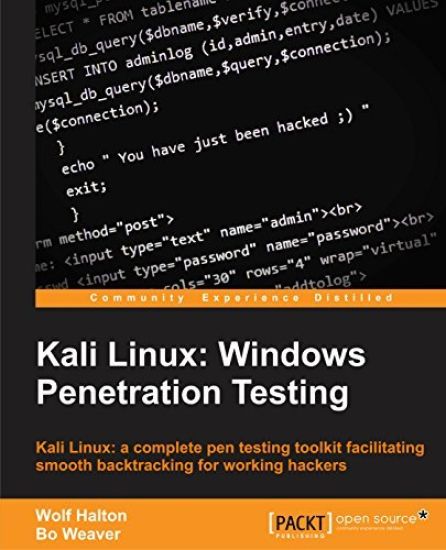
Kali Linux: Simple and Effective Approach to Learn Kali Linux
Ethan Thorpe
Independently Published
2019
nidottu
The Kali Linux book is a beginner's introduction to Kali Linux. In today's world, security is one of the most important talks of the town. It is necessary to secure the infrastructure that powers the world around us. Kali Linux aids in the vision of a secure world where everything is connected. It is a penetration testing operating system used by professionals all around the world. The book can be used by anyone who has an interest in Linux, Hacking, Security, Pentesting, and others, and will act as a good starting point to work with Kali Linux. After reading this book, you will be able to work optimally with Kali Linux and make the most out of what Kali Linux has to offer. The book contains a practical approach to understand the different aspects of Kali Linux. It starts with a basic introduction to Kali Linux, followed by understanding how the hacking process works, and then understanding cybersecurity concept. With this core understanding, we then move to how Kali Linux is connected with Debian. To help new beginners, we also cover Linux Fundamentals. Next, our focus completely changes to what Kali Linux offers. We learn about Kali Linux configuration, documentation, community, security, monitoring, security assessment, and tools. In this book, you will learn the following: Kali Linux introduction and installationIntroduction to hacking and hacking processLearning cybersecurity conceptsLinux fundamentals refreshKali Linux configurationKali Linux Documentation and CommunityDebian Package ManagementKali Linux Security AssessmentKali Linux ToolsNetwork ScanningAll the topics are covered in-depth to enhance your knowledge. By reading the book, you will be able to use Kali Linux as your daily driver and understand what makes it so awesome