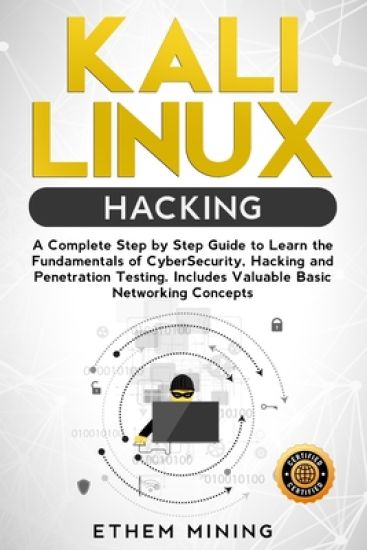
Are you on a quest to evolve into a savvy cybersecurity expert, keen on mastering the core essence of ethical hacking? Is your aim to gain a thorough grasp of the robust tools offered by the premier Linux distribution for ethical hacking? Have you rummaged through the digital realm seeking that impeccable resource to jumpstart your hacking journey, only to find yourself entangled in a web of scattered, perplexing information on hacking and cybersecurity? If a resounding 'yes' echoes to any of these inquiries, then you've just stumbled upon your treasure - this book is crafted precisely for you Updated and Edited Version The hacking realm is morphing; it's becoming an enigmatic, sophisticated field. As the digital threats loom, corporations are in a frantic race to shield their digital treasures, establishing formidable cybersecurity fortresses. However, the real efficacy of these digital shields is in their relentless testing and fortification against emerging threats, a task bespoke for the gallant knights of the modern era - the penetration testers and ethical hackers. These are the code-warriors trained to discover, exploit, and mend network vulnerabilities. The corporate demand for these skilled penetration testers and cybersecurity maestros, armed with hands-on prowess in Kali Linux and other open-source hacking arsenals, is soaring sky-high. Now is your opportune moment to dive in, and this book is your golden ticket into this enthralling realm. Unlock a trove of wisdom as you traverse the pages of Kali Linux Hacking. Journey from the basics, with no prior knowledge required, ascending gradually to the pinnacle of practical know-how on wielding Kali Linux and other open-source tools, morphing you into a formidable hacker. Get a taste of what successful penetration testing entails, all elucidated in a simple, engaging manner. Peek inside, here's a snippet of the treasure awaiting you in Kali Linux Hacking: A crisp unveiling of 'hacking' and the magic of Kali Linux.A deep-dive into the myriad hacking types, spanning from session hijacking, SQL injection to phishing, and DOS attacks.Debunking the myth of the malicious hacker and introducing the 8 modern-day hacker personas.Unveiling why Kali Linux is the darling platform for both budding and pro hackers.A step-by-step manual to set up Kali Linux, mastering the Linux terminal, and essential Linux commands.An exhaustive guide on leveraging Nmap to identify, comprehend, and exploit vulnerabilities.Mastering the art of stealth in hacking and penetration testing.Elevate your hacking finesse with Bash and Python scripting.... and a whole lot more Kali Linux Hacking is your companion in launching your hacking odyssey. It's meticulously tailored for the total beginners, interspersed with practical examples and real-world hacking methodologies, all elucidated in plain, lucid English. This book is the emblem of the 21st-century hacker and cyber defender and is your springboard to escalating your skills in cybersecurity and pen-testing. Whether you're a hacking neophyte, gearing up for a thrilling career shift into cybersecurity, or aiming to be a magnet for lucrative job offers, Kali Linux Hacking is your quintessential guide. Yearning for more? Hit Buy Now With 1-Click or Buy Now to embark on this exhilarating adventure